If you are reading these lines, you have probably heard about uPress’s overplayed cyber-attack (more why it was overplayed later). uPress is an Israeli web hosting company specializing in WordPress hosting, among its customers are restaurants, municipal authorities, small businesses, etc. They also offer WordPress development and design services.
Why WordPress is so popular
WordPress is one of the biggest open-source Content Management Systems (CMS) on the internet, developed in PHP. According to W3Techs, 37% of worldwide web sites are using WordPress. Some of the reasons for that are:
- WordPress is an open-source CMS, so it constantly gets new updates, themes, and designs.
- There are more than 50,000 plugins that help the website owner create a more flexible and functional website.
- Installing a WordPress website is very easy, and generally, you do not have to write even a single line of code to build a professional WordPress website.
- And of course, most importantly, it is free.
Understanding the attack and common vulnerabilities
As a matter of fact, the cyber-attack against uPress was defacement of the WordPress websites hosted in uPress. It means that the attack was not too sophisticated, and the attacker only changed the visual appearance of the websites. The attack was only possible because:
- uPress used vulnerable out-of-date WordPress plugin which had security issues.
- uPress is one of the biggest WordPress hosting companies in Israel and when the attacker managed to exploit this vulnerable plugin, they had access to all the websites hosted on the server.
uPress is not the only one susceptible to this weakness. In October 2019 Amit Serper (@0xAmit) , a researcher from Cybereason, tweeted that none other than Cisco, exposed their WordPress installation file to the internet.
In this case, when the installation file is exposed to the internet, any user may modify the configuration of the specific WordPress website
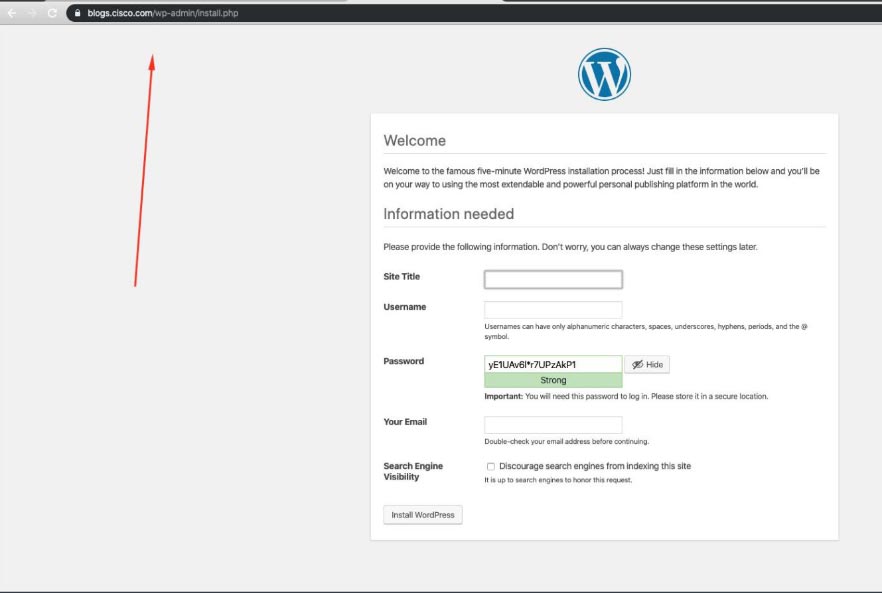
(asset by Amit Serper)
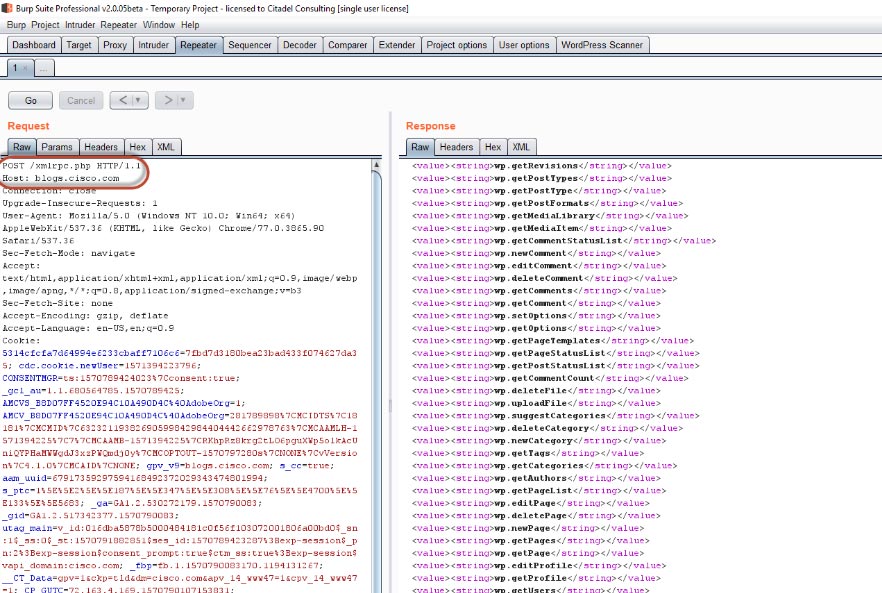
Cisco also exposed the xmlrpc.php file which could lead to brute force attacks against the system.
When the xmlrpc.php file is exposed to the internet, a malicious user may conduct brute force attack against the admin account. This attack will not be monitored as xmlrpc is a legitimate function within the WordPress website.
Essential steps to secure your WordPress website
Although it is very easy to install and operate a WordPress website, when it comes to security, things get a bit more complicated. here are some measures you must take:
- Always keep your plugins up to date, WordPress will notify you when there are available updates. Most of the time, you will not need to do anything besides pressing the ‘update’ button. Sometimes changes in the web site design will be required.
- Do not expose sensitive URL paths such ‘wp-config.php’,’install.php’, ‘wp-json/wp/v2/users’.
- Adjust the WordPress PHP code to block automated scanners from scanning your WordPress website for vulnerable plugins, themes, core version user enumeration, etc.
- Block any unauthorized access to the xmlrpc.php file (an attacker can exploit it to establish a brute force attack against high privileged users).
- Only allow specific IP addresses to access the WordPress login page /wp-login.php. If you cannot do so, implement a CAPTCHA test or set a limit on the number of possible attempts to log in.
- When installing a fresh WordPress website, do not set a generic username like ‘admin’. And no, ‘qwerty’ as a password is not an option. Use a unique username and a strong password.
- Block Google crawler from indexing sensitive paths like “wp-config.php” or the plugins folder path by adding them to the “Disallow” section in the robots.txt file
- Install one of WordPress’s “Firewall” plugins, like Wordfence.
conclusion
WordPress websites can never be 100% secure, but the more actions you will take to secure your website, the fewer security issues you are likely to face. Do not ignore the red flags, especially in relation to one of the most common CMS worldwide.





